AsiaBSDCon 2026 Recap

Last week I was in Taipei, Taiwan, for the FreeBSD Developer Summit and AsiaBSDCon 2026. Here's how it went.
Devsummit
The Developer Summit ran for two days, 10 AM to 5 PM each day. Most sessions were short presentations covering topics like FreeBSD on WSL 2 and Ansible on FreeBSD. Between talks, developers worked on patches, followed up on mailing-list threads, and reviewed one another's work — I got some useful feedback on my LLVM pull requests during these gaps.

The AsiaBSDCon organizer handed out Kuai Kuai, a popular Taiwanese snack that comes in a bright green package. The tradition is to place it on top of your computer as a good-luck charm — the idea being that your code won't break as long as the snack hasn't expired. Think of it as the Taiwanese equivalent of holding a blessing ceremony in a server room before it goes live.
So I guess it's something similar to having religious ceremony in a server room before it opens to public.

AsiaBSDCon 2026
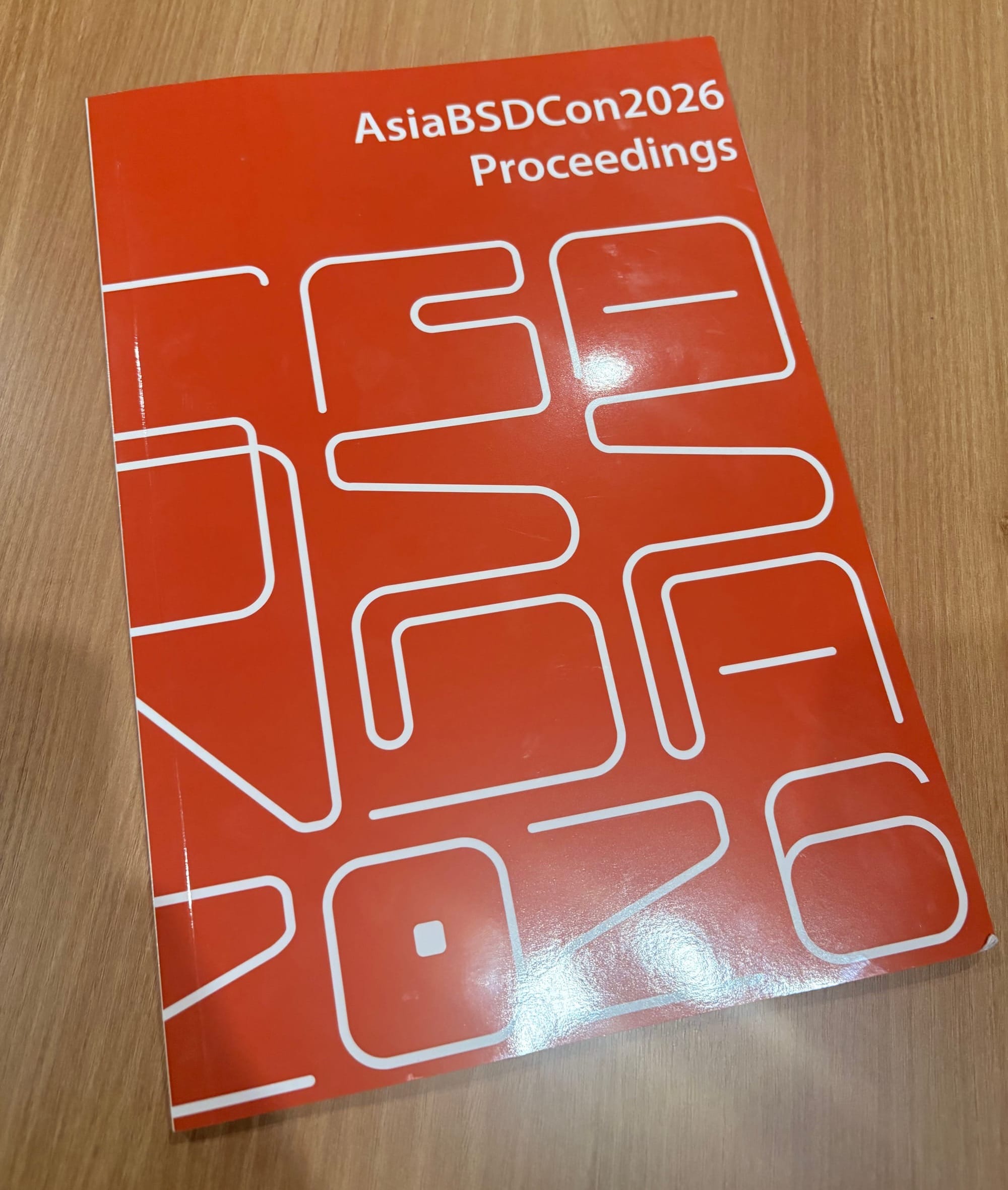
The main conference began right after the summit and drew roughly three to four times as many attendees. Each participant received a copy of the AsiaBSDCon 2026 Proceedings as part of the welcome package. The book itself was well produced, though the formatting across papers was inconsistent — most followed the IEEE Conference template, but font weight, size, margins, and layout varied noticeably, and a few papers used entirely different templates. It would be great if future committees provided a strict template and enforced compliance. A PDF or EPUB edition would also be a welcome addition.
Talks That Stood Out
Rethinking the forms of OS functionality development
Kenichi Yasukata presented his work on a portable userland TCP/IP stack. He outlined the performance advantages of running the network stack in userspace but highlighted a persistent challenge: portability across operating systems due to divergent APIs.
His solution is a userland TCP/IP stack that deliberately omits OS-specific code. That sounds paradoxical — how can a TCP/IP stack function without OS bindings? The answer is that developers supply the OS-specific low-level glue themselves. This separation lets the core stack remain portable while still achieving strong performance.
Kenichi also discussed techniques for intercepting system calls without relying on LD_PRELOAD. His approach uses binary overwriting, which requires architecture-specific hooks: svc-hook on arm64, and zpoline (a trampoline through an alternative syscall entry point) on x86-64.
Faster, smolBSD! Boot! Boot!
Pierre Pronchery showcased smolBSD, a container-oriented NetBSD variant. By stripping the kernel down to only the necessary drivers and bypassing the traditional UEFI boot path, smolBSD achieves bare-metal boot times under one second.
Pierre demonstrated PicoClaw and SSH server images that can be instantiated much like Docker images — an impressive feat for anyone who has waited several seconds for a standard container to come up. He also showed ZFS-on-root running on NetBSD, though this still appears to lag behind FreeBSD's mature ZFS support.
Run Time Reoptimization for Modern Heterogenous Systems
George Neville-Neil argued that modern hardware — CPUs, GPUs, NPUs — has evolved far beyond the PDP-11 model, yet Unix-like operating systems still carry assumptions rooted in that era.
He dove deep into CPU microarchitecture: cycle-level penalties, cache misses, branch mispredictions, and the like. The core idea is to capture these runtime penalties and feed them back into LLVM, which he highlighted as a strong abstraction layer across diverse hardware targets. This feedback from live profilers is passed through optimization pipelines that produce architecture-specific binaries, which are reloaded without exiting the program.
I'll admit this talk was hard to follow in real time — partly because I was multitasking — and I plan to revisit the recording to better understand the benchmarking results.
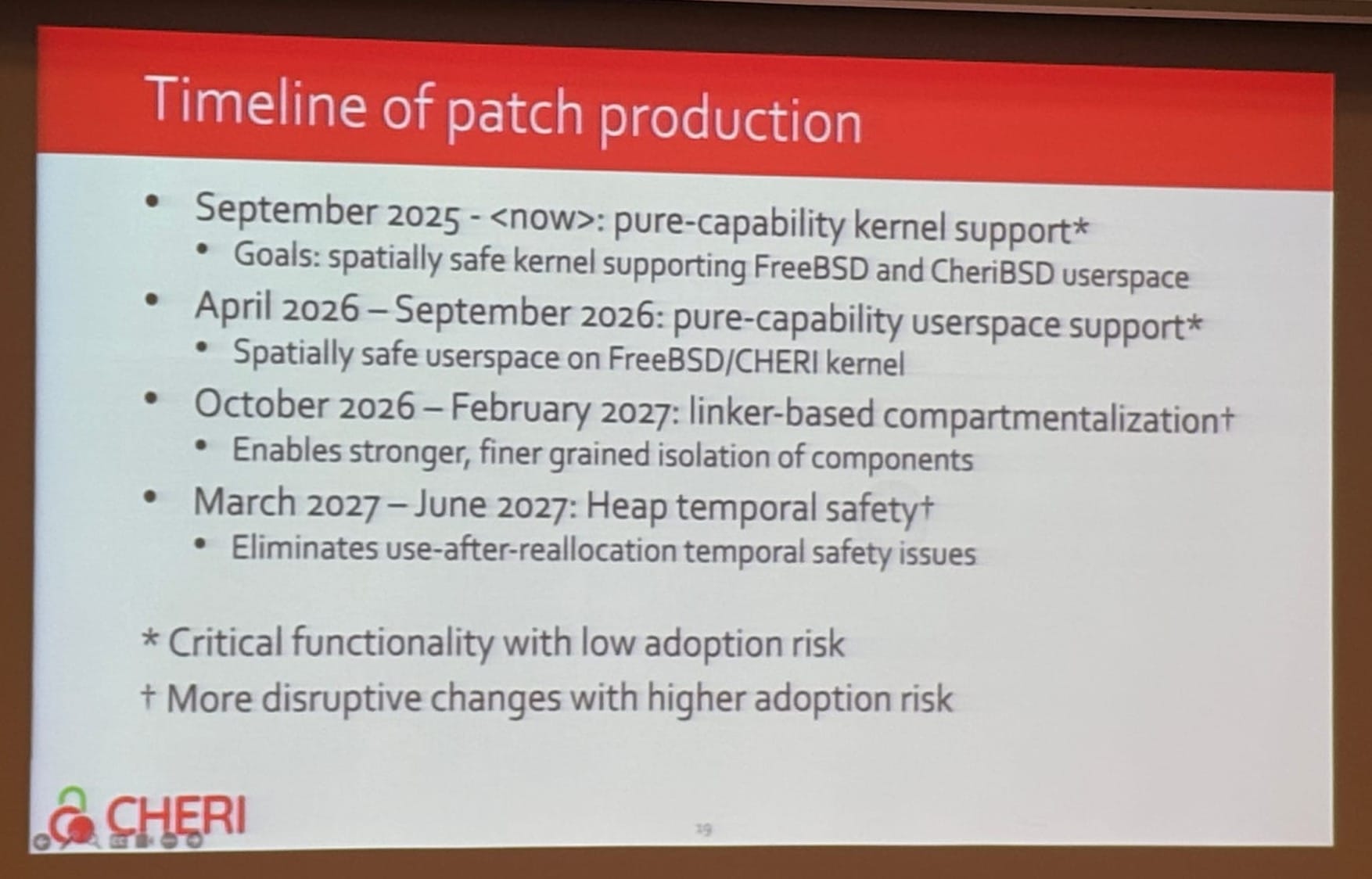
Bringing memory safety to BSD with CHERI
Brooks Davis presented the CheriBSD upstreaming effort, with a strong emphasis on CHERI's security benefits. Two examples stood out. First, the team asked an LLM to inject 13 memory bugs into NGINX; CHERI caught all 13 plus two additional bugs the LLM introduced unintentionally. Second, while porting Chromium to CheriBSD, the two-person team uncovered numerous memory vulnerabilities that were later assigned CVEs — matching or exceeding the output of over 100 security researchers on the Chrome team, thanks to CHERI's memory-safety guarantees.
The upstreaming roadmap targets completion by FreeBSD 16, expected in December 2027. CheriBSD will be the first time-sharing operating system with full CHERI support, covering both Arm Morello and RISC-V CHERI (RV64Y). On the Linux side, a CHERI port is in progress, but organizational challenges — what I'd describe as significant process and priority shifts — appear to be slowing adoption.
What's Next?
BSDCan 2026 — I'll be presenting a talk on hybrid scheduling. Unfortunately, a midterm exam will keep me from the hackathon.
EuroBSDCon 2026 — I'm eager to attend, pending travel approval from my second co-op employer.
AsiaBSDCon 2027 — During the closing session, Li-wen Hsu announced that next year's conference will be held in Singapore. As George put it, making it happen requires "volunteers, volunteers, volunteers — and sponsors, sponsors, sponsors." If you're based in Singapore and can spare four days, please consider volunteering. If your company is in a position to help financially, sponsorship goes a long way.
Acknowledgments
As George Neville-Neil noted in the closing session, enormous thanks are owed to Li-wen Hsu (lwhsu@) for making AsiaBSDCon possible. Everyone who worked alongside him knows the effort he poured into the event, day and night. Thank you, Li-wen.
I also want to thank the FreeBSD Foundation for approving and sponsoring my trip to Taiwan.